This Week in Software Supply Chain Security: April 18 - April 24, 2024
Trail-of-Bits-tool-o-rama week
Welcome to This Week in Supply Chain Security, your essential weekly resource for the latest developments in software supply chain security. Each week, we bring you critical insights and updates to help you stay ahead in safeguarding your software supply chain. Brought to you by the open source security experts at Stacklok.
🚨 Recent Security Incidents
A selection of the most impactful security breaches or threats in supply chains
Abusing GitHub’s File Uploads
MacAfee reported on a new malware campaign which leveraged files uploaded through issue and PR comments. Using the “file upload” GitHub feature, the attached files were available at https://github.com/{org}/{repo}/files/{id}/{name}. These files can be uploaded even if the comment is never submitted on GitHub, and then distributed through GitHub’s CDN. Repo owners cannot see or manage these files, though GitHub can remove them if reported. Be careful about trusting files just because they look like they are part of a trusted repo’s URL pattern!
Scanning GitHub Actions for Fun And Profit
Another study of GitHub Actions vulnerabilities that can lead to bug bounty payouts from Adnan Khan. In this case, it was a vulnerability in a Google OSS repo which had laid dormant for almost 4 years. The writeup includes some impressive work to avoid StepSecurity’s harden-runner tool by handling both the payload and the exfiltration using GitHub’s APIs. Worth a study if you’re considering using GitHub Secrets in your public PR workflows.
Dependency Confusion In The Wild
Legit Security detected a dependency confusion vulnerability in Cordova App Harness, an archived Apache project. As a refresher, dependency confusion occurs when a project’s private dependencies can be replaced (hijacked) by malicious versions uploaded to public repositories like NPM. In this case, the researcher was able to claim the vulnerable dependency name and discover at least 100 downloads in the first 3 days despite the project being archived (not receiving further updates). Software that’s archived is like milk that’s been in the fridge too long — it’s not worth the risk.
Tea.xyz Causing Headaches
RubyGems (and Web3 Is Going Great) reported on recent attempts to abuse the Tea protocol to collect cryptocurrency rewards by publishing a large number of empty packages which all link to each other. For those of you not in the cryptocurrency space, the Tea protocol aims to incentivize open-source developers by rewarding them with a cryptocurrency based on their open source contributions. Shockingly, this instead leads to scammers attempting to capitalize on a “giveaway”. Several folks at Stacklok also noticed this pattern and have been working with GitHub on cleanup there.
💡 Free Tools and Tips
New open-source and free (as in beer) supply chain security news
Don’t Get Too Attached To This Tool
Google released a (go) library for scanning filesystems to find installed language packages called osv-scalibr on GitHub this week. The README says:
Note: The code in this repo is subject to change in the near future as we're merging SCALIBR with OSV-scanner to provide a single tool that unifies the two scanners' extraction and vuln scanning capabilities.
Yep, that’s right — don’t depend on this library because it’s going to get merged with another Google tool. Still, here’s your early preview notification if you like to get messy with language filesystems and SPDX.
Audit Like Trail of Bits
Trail of Bits has released weAudit on the VSCode marketplace. While not directly a supply-chain security tool, it provides a bunch of handy tools for source code audits, which are part of ensuring that your software supply chain is secure. Features include the ability to highlight and make notes on various sections of code, as well as collaborate with other auditors and mark files as reviewed.
More Trail of Bits Tools
Trail of Bits also open-sourced the cargo-unmaintained tool to find unmaintained cargo packages in the dependencies of Rust projects. Memory safety is no match for code that’s just not going to get any more fixes.
👀 Community and Public Sector Updates
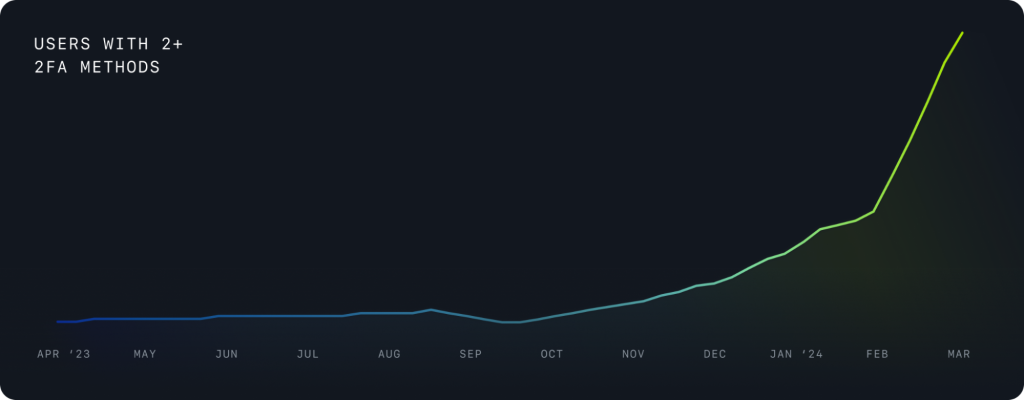
GitHub’s 2FA Rollout
GitHub reported on the status of their efforts to roll out second-factor authentication (2FA) to all people contributing code on GitHub. According to GitHub’s numbers, 95% of users who received the 2FA requirement managed to complete the enrollment, with the vast majority of WebAuthn users choosing to use Passkeys as a second factor. (It’s not clear how SMS and other 2FA methods compare — the post has a number of congratulatory back-pats, but all the numbers are percentages in a way that makes it hard to find your own data…) Still, good job on GitHub for increasing 2FA usage — if you’re on GitHub, you should turn those second factors on!
How much is Free worth?
A Harvard Business School paper estimates the “demand-side value” (i.e. value to consumers) of open-source software at $8.8 trillion. The “supply-side value” (amount paid) is only $4.15 billion, which means that every dollar invested in open-source has a $2000 payback across the world. Pretty inspiring, if true.
That’s all for this week! See you next Thursday…