Welcome to This Week in Supply Chain Security, your essential weekly resource for the latest developments in software supply chain security. Each week, we bring you critical insights and updates to help you stay ahead in safeguarding your software supply chain. Brought to you by the open source security experts at Stacklok.
🚨 Recent Security Incidents
A selection of the most impactful security breaches or threats in supply chains
VSCode Malware Reaches Hundreds of Organizations
Israeli researchers built a copy of the “Dracula Official” VSCode extension, registered it at a typo name (including verifying a typo domain name), and added phone-home capabilities (but no actual malware). What they found next will surprise you not at all. Thousands of developers downloaded the extension from the Microsoft VSCode marketplace, including billion-dollar companies and a country’s court network. The extension was also listed in the “trending” section of the marketplace for a while. Poking further, they found over a thousand extensions with known malware in their dependencies, and a bunch of other stats in part 2. Part 3 describes how to hack your way to the top of the extensions recommendations; parts 4-6 are on their way. Apparently Aqua Security found this a year ago as well.
New York Times (Source Code) On 4Chan
A hacker posted thousand source code repos stolen from The New York Times; reporting at BleepingComputer. The total size of the leak was 270GB; a README in the tar file indicates that the attacker stole a GitHub token in January in order to download the repos. The Times has since revoked the token, and claims that the stolen code has not affected its operations. Guess they’re doing better than the 38TB leak from Microsoft last year.
GitLoker is Ransomware for GitHub
BleepingComputer reports on a threat actor who is wiping GitHub repos and requesting a ransom for the restoration of the data. The repo is renamed and the contents replaced with a single README.md file with Telegram contact information. The suspicion is that the attackers are using stolen GitHub credentials to perform these attacks. Given the distributed nature of Git checkouts (clients can re-push the files to the server), it’s unclear how much damage is being done. Still, it would be scary to wake up and see all your data removed from GitHub.
NPM Cache Poisoning To Block Downloads
The security research team at Lupin & Holmes found a denial of service attack on npm. An attacker could poison the HTTP cache for file downloads, causing npm install of a targeted package to fail as long as the attacker kept up the cache-poisoning attacks. This is only a DoS, so it seems less critical than replacing the URL, but it would still be a lousy day for anyone attempting to build javascript code.
Typosquatting on PyPI Targets Crypto Utility
Sonatype reports on a typosquatted attack on crytic-compile, a popular python utility. The attackers even aligned the version numbers with the real library, picking up where the original library left off. Unfortunately, the malicious library drops a copy of the Lumma malware to steal cryptocurrency wallets on Windows.
Your Crypto Isn’t Safe at NPM, Either
Phylum also got in on the action of supply chain attacks against crypto developers with a report on a React kitchen-sink library which attempts to steal crypto credentials from browser extension files. The library also downloads some python code to maintain persistence and capture keystrokes and clipboard contents, and has its own home-rolled obfuscation code. Another reminder to check the tools you’re downloading before you just grab something that looks good.
How Long To Compromise?
Stacklok (my employer) published a blog post about detecting a typosquatting attack on the Python requests package. The interesting thing is that despite being detected within hours, the package had already been downloaded hundreds of times. Pretty scary that a typo can spread so quickly — it would be interesting to see more analysis of how these attacks spread.
💡 Free Tools and Tips
New open-source and free (as in beer) supply chain security tools
Govulncheck removes VEXing CVEs
The govulncheck program released by the Go language team can now export OpenVEX as well as SARIF data about which vulnerabilities are actually reachable from the compiled code. Because govulncheck is tied in with the Go compiler, it can flag that certain library vulnerabilities (for example, in certain functions or dependencies) are never reached by particular calling code. The hope is that many of the pesky transitive vulnerabilities based on library CVEs found by tools like Snyk can be weeded out using VEX statements that show that the vulnerability is not reachable. It’s definitely nice to see that the language authors are on the side of reducing CVE noise!
Reproducible Docker Builds
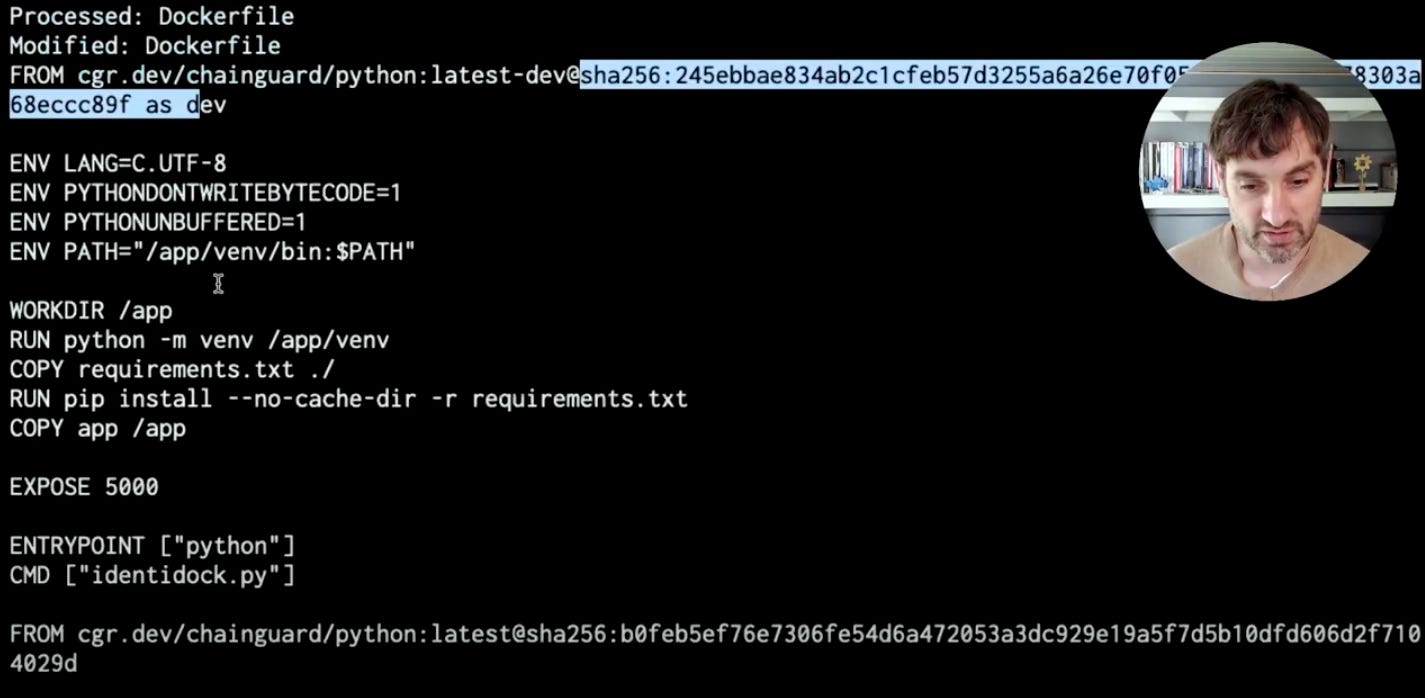
Chainguard’s Adrian Mouat has a video where he breaks down some of the problems that can occur when coming back to a Docker build after a few months away. Tags may shift, and Python library versions may also change. Adrian uses stacklok/frizbee and chainguard-dev/digestabot to pin the Dockerfile images and then update them in a controlled fashion, and pins his dependencies with pip freeze.
👀 Community and Public Sector Updates
Explaining CVEs, NVD, and KEV
Kyle Kelly wrote an explainer on how the different vulnerability management platforms supported by the US government and private sector interoperate. If you’ve been confused about how the NVD (National Vulnerability Database) relates to CNAs (CVE Numbering Authorities), this might be the catch-up you need.
Ubuntu Security Notices Now In OSV
Canonical announced that it is publishing its security advisories in the OSV schema, and is adopting some of the tooling built by the OpenSSF Vulnerability Disclosures Working Group. It’s nice to see security standards coming together!
That’s all for this week! See you next Thursday…