This Week in Software Supply Chain Security: June 13 - June 19, 2024
More New Good Stuff Than Bad!
Welcome to This Week in Supply Chain Security, your essential weekly resource for the latest developments in software supply chain security. Each week, we bring you critical insights and updates to help you stay ahead in safeguarding your software supply chain. Brought to you by the open source security experts at Stacklok.
🚨 Recent Security Incidents
A selection of the most impactful security breaches or threats in supply chains
Hijacking GitHub-Hosted Runners With Self-Hosted Replacements
Synaktiv documents how they started with developer-level access to a GitHub organization, and were able to move from a vulnerable action on a self-hosted runner in a low-privilege repository to reading secrets on a separate high-security repo that the developer did not have access to. The intermediate steps involve a GitHub App with permissions to register self-hosted runners (probably used to by the self-hosted runner to register itself) and registering a runner under the ubuntu-latest tag at the org level. While this targets a particular CI configuration, it seems that GitHub is a bit remiss in not protecting the ability to re-register well-known tags. No CVE or vulnerability report is mentioned, so no idea if this will be fixed.
It’s Not a Cute Body Pillow: Sleepy Pickle
Trail Of Bits described a new ML model exploitation technique to target the use of Python pickle files to distribute ML models. Rather than directly executing Python code in the target environment, Sleepy Pickle targets the ML model, compromising either the model weights or the input and output transformations. The malicious pickles can also corrupt the process of loading other models, allowing for a compromise of existing models if the two are loaded at the same time. They demonstrate three attacks on models: injecting harmful information, exfiltrating existing user content, and injecting malware links into responses. The conclusion is that ML models need to move away from pickle as a file format, and separate code and model weights into separate content.
💡 Free Tools and Tips
New open-source and free (as in beer) supply chain security tools
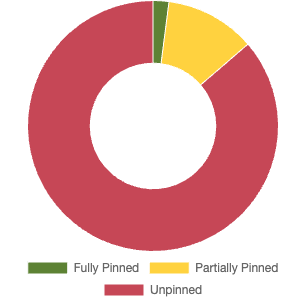
Pin Floating Tags to Digests with Frizbee
Stacklok (my employer) has added a GitHub Frizbee Action to assist with pinning GitHub Actions and container images to specific content digests rather than (mutable but human-readable) tags. While the human-readable tags are great for humans, they are generally able to be changed by owners of the resource. This means an attacker could change the v4.2 tag (for example) to point to a vulnerable input to your build pipeline. Pinning to specific digests helps to avoid this attack; tools like Dependabot and Renovate can still send PRs to update dependencies on purpose, but upstream supply chain projects can no longer change your CI without action on your part.
Flux is Publishing VEX
According to this post on X, the FluxCD project is publishing VEX documents to document CVE exceptions as part of their vulnerability triage process. The VEX documents are checked in to source control, so there’s still a little bit of a “connect X to Y” problem for you to solve, but they’ve already classified 5 vulnerabilities as “not affected”, so it’s nice to see folks starting to adopt these solutions to quieting the CVE noise.
Maybe a Fun Weekend Project?
Kornel Lesiński shared an intriguing toot on Mastodon with data containing comparisons of crates.io Rust crates with their claimed git repositories. Unfortunately, Kornel didn’t have time to do much analysis, so he’s dumped the output he has so far along with the analysis code in hopes someone does something with it.
Safely Using Regular Expressions
The OpenSSF’s Best Practices working group has released a guide on using regular expressions safely. The guide points out a bunch of interesting quirks of different regex engines, as well as the dreaded “Regular Expression Denial of Service” risk with popular backtracking implementations in Java, JavaScript, Python, and elsewhere. ReDoS is particularly pernicious as a contributor to CVE noise, so it’s nice to see some guidance on how to avoid it.
👀 Community and Public Sector Updates
What’s in the SOSS? Podcast
Despite the terrible “sauce” pun in the name, the OpenSSF has gone ahead and started a weekly podcast series interviewing various folks in the supply chain security space. Current episodes include insights from Red Hat, Google, Microsoft, OpenAI, Intel and Stacklok. From having worked with 3 of the names directly, I can say that they’ve got some impressive insights on what’s going on in software security and concrete steps we can take to steer software towards being more secure. Episodes are 15-20 minutes each, and episodes include transcripts for those of you who prefer to read over listen.
Toyota Wants Safety-Critical Rust
The Rust Foundation announced a 10-company collaboration to develop infrastructure for using Rust in safety-critical software — think “antilock brake controllers” and other industrial uses. The efforts include not only guidelines, but tools such as linters and static analysis tools, and all such tools will be submitted upstream under a similar license to Rust itself. The group is also looking for additional members and contributors, so if you fancy yourself a software-safety aficionado and a Rustacean, you know where to find your peeps.
That’s all for this week! See you next Thursday…