This Week in Software Supply Chain Security: September 12 - September 18, 2024
The bad supply chain news this week was not in computers.
Welcome to This Week in Supply Chain Security, your essential weekly resource for the latest developments in software supply chain security. Each week, we bring you critical insights and updates to help you stay ahead in safeguarding your software supply chain. Brought to you by the open source security experts at Stacklok.
🚨 Recent Security Incidents
A selection of the most impactful security breaches or threats in supply chains
CloudImposer: Dependency Injection on GCP
Tenable Research discovered a dependency confusion attack in Google’s documentation on using --extra-index-url to add private package repositories. Vulnerable customer projects that used this argument to add their own private artifact repositories could be attacked by registering the same name and version number (or a higher version number) in the public PyPI repository. The researchers also found that the Google Cloud Composer images used this argument to fetch a Google-private package, and were able to exploit that to run code on Cloud Composer. The confusing package was taken down by PyPI within 30 minutes, and Google fixed both their documentation and Cloud Composer tools shortly thereafter. The pip install improvements are still stuck in PEP-land at the Python Software Foundation, though.
💡 Free Tools and Tips
New open-source and free (as in beer) supply chain security tools
Blocking Unauthorized Android Installs
Google has recently launched the “Google Play Integrity API” to allow apps to determine whether or not they have been installed through Google’s app store. This will allow application authors to check whether the runtime environment is secure, including both system attestation and an origin check on the application install itself. While this sounds very Big-Brother-ish, it can also be used to warn users who may have installed the app through a third-party mechanism which may have also delivered unwanted malware. But yeah, a lot of it is mostly about content protection controls.
WordPress to Require 2FA For Authors
2FA and SVN-specific passwords are coming to WordPress.org on October 1. The SVN-specific passwords are being introduced because the underlying Subversion software does not support 2FA — instead, users will need to use the newly-generated high-entropy passwords when deploying manually or through automation. Given the number of websites that rely on WordPress, the additional security seems like a welcome improvement, though there’s no mention of signing or other integrity-verification tools for plugin authors.
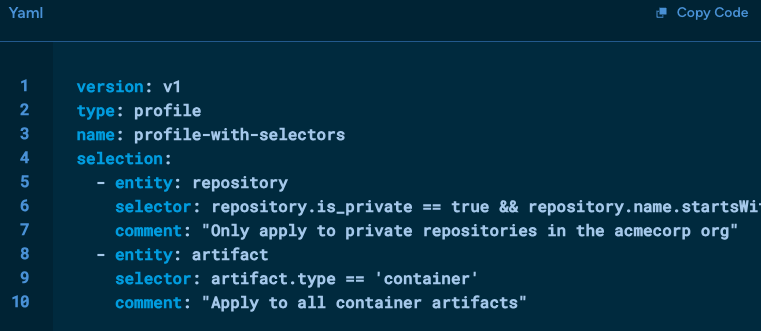
Policy Selectors for Minder
Stacklok (my employer) has added support for selectively applying Minder policies using resource properties and a filtering language. The filtering language is CEL (Common Expression Language), which may be familiar to users of Google Cloud products; they show examples of filtering based on repo forks, artifact type, license, and pull request author. Minder is open-source, but you can also use https://cloud.stacklok.com/ for free on public repositories.
👀 Community and Public Sector Updates
SANS and AWS Want You To Build In Security
Or, at least, AWS is highlighting a new whitepaper in collaboration with SANS on Secure by Design. The 16-page doc is fairly high-level, covering the difference between Secure by Default and Secure by Design, as well as covering a range of topics including threat modelling, culture, and automation. There’s even a special reward if you get to the end of the document…
Tips On Non-Actionable Security Findings
Google’s Bug Hunters blog has some tips on how to determine whether your security scanner is generating security findings that aren’t relevant. TL;DR - a lot of scanners don’t look at the difference between upstream software and vendor-specific patches and guidance, and the Linux vendors actually do a lot of work to filter out CVEs before you need to update software (for example, because they didn’t build with that option or issued a smaller patch than the upstream). Also, a lot of the vulnerability data is noisy — for example, not including version numbers, or point-in-time copies of information which has since changed. NVD, we need you!
That’s all for this week! See you next Thursday…