This Week in Software Supply Chain Security: July 25 - July 31, 2024
More Hardware In Your Software Supply Chain!
Welcome to This Week in Supply Chain Security, your essential weekly resource for the latest developments in software supply chain security. Each week, we bring you critical insights and updates to help you stay ahead in safeguarding your software supply chain. Brought to you by the open source security experts at Stacklok.
🚨 Recent Security Incidents
A selection of the most impactful security breaches or threats in supply chains
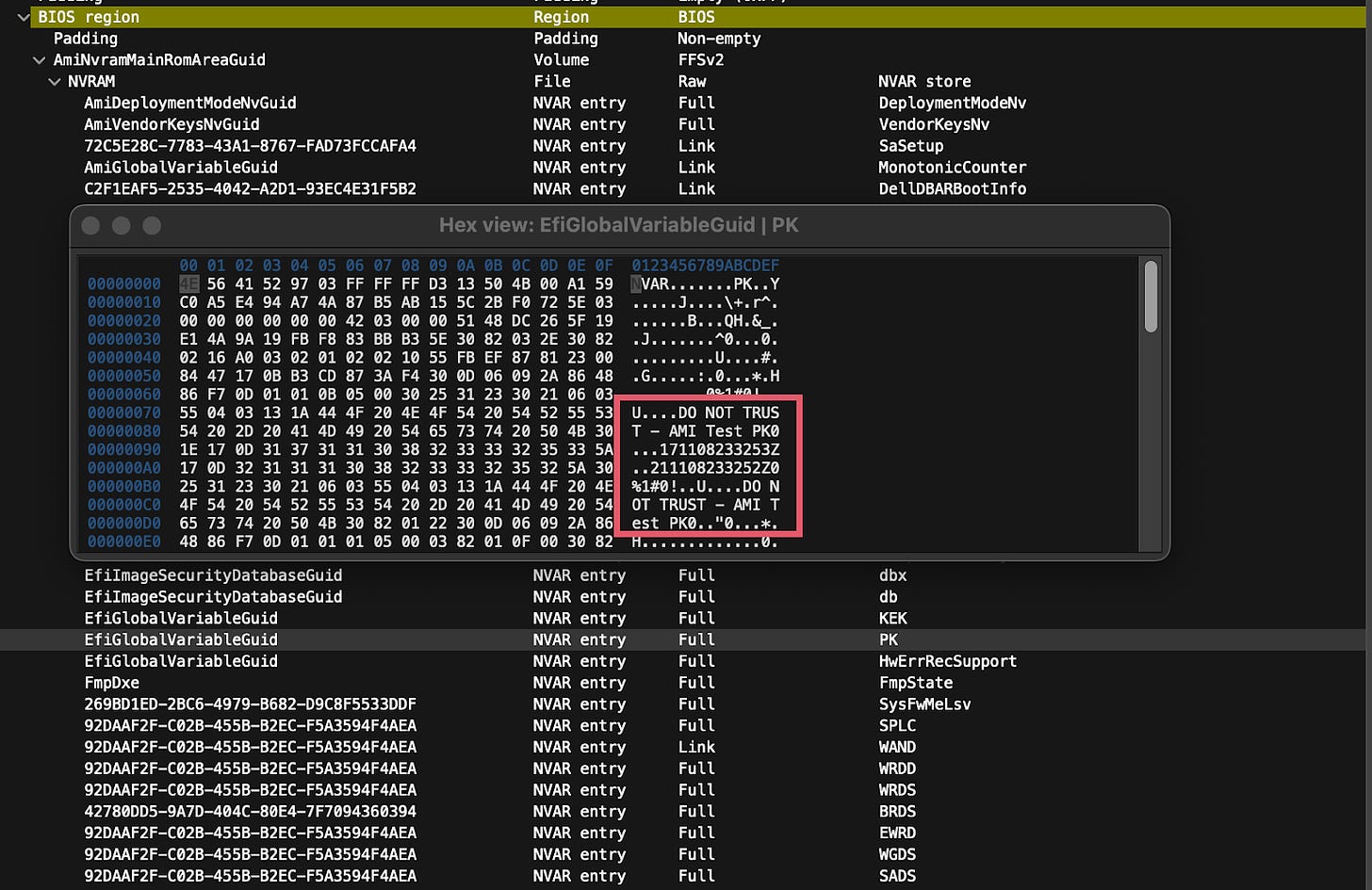
“DO NOT TRUST”? Sounds Good To Me!
Binarly discovered a private key trusted by a number of Secure Boot hardware platforms on GitHub, protected by a 4-character password (anyone want to start a pool on what those 4 characters were? It’s fun to guess). While the key was a test key, the corresponding certificate was trusted by at least 5 hardware vendors. Ars Technica has a more accessible write-up, but the TL;DR is that at least 5-10 vendors ignored Secure Boot best practices and shipped multiple platforms that either used the exposed platform key, or used other broadly-shared testing keys labels “DO NOT SHIP” or “DO NOT TRUST”. These platform keys are supposed to be unique for each product and rotated regularly, to reduce the exposure if compromised. A number of the 800+ affected models are no longer under support, so whether or not they get a new BIOS with a new list of trusted keys is anyone’s guess.
Build Me an Army!
Check Point Research published observations of a network of GitHub accounts which seem to be operated by a central group. The accounts distribute malicious links and content, and also star, fork and otherwise interact with repos created by each other. The assumption is that the 3,000 accounts involved are one of possibly several networks offering malware distribution services.
GitHub’s Long Memory
Truffle Security posted about how GitHub stores and shares commit data across a source repo and the pool of repo forks. The end result is that you can access commits on forks which were deleted and never merged upstream, or access commits from forks of private repos when the source repo is made public. This is a fundamental part of GitHub’s underlying Git implementation, assisted by GitHub’s willingness to expand short SHA hashes to complete hashes, as long as the SHA hash is unique. Truffle used this to find some secrets checked in to repo forks, but there’s probably also other interesting espionage techniques available.
Building More Than a Function
Tenable reported a vulnerability in Google’s Cloud Functions build environment that allowed a user to escape from the Cloud Functions-specific build environment into the larger Cloud Build environment, potentially attacking other CI environments or other cloud resources. Build services are an attractive target for attackers, as they are effectively “Remote Execution as a Service” by design. This one has been patched for new accounts, but if you have an existing account where you expect Cloud Functions authors to have less than full build permissions, you may want to check out the report.
MacOS and GCP Popular Enough to get their own Malware
Checkmarx published a report on a malicious python package targeting Google Cloud Platform credentials files on MacOS. The attack also targeted specific platform UUIDs, so this was either testing or a very targeted attack. Checkmarx also highlighted some possible impersonation / social engineering indicators, though it’s not clear how they were involved based on the report.
When The Supply Chain Stops, What Happens To Your Car?
Wired has a short article about how remote connectivity and software updates are going for automakers. The short version: some automakers got caught out by the retirement of 3G telco networks in the US and elsewhere, and the 10-20 year car lifecycle is much longer than that of a smartphone or PC. It’s not clear how well automakers (or the public) are prepared to handle the extended compatibility (and security) needs of automakers. Most other industrial use cases (airplane, hospitals, factories) is in a much more controlled environment; I definitely don’t want to be thinking about which cars on the road are vulnerable to a 3-year old CVE because the manufacturer won’t build a new release.
💡 Free Tools and Tips
New open-source and free (as in beer) supply chain security tools
Making Homebrew Safer
Security company Trail of Bits has audited the popular (at least on Macs) package manager Homebrew. Despite currently mostly serving CI-built binary bottles, the core of Homebrew contains some very dynamic Ruby code, including a home-brewed (ha!) DSL. Trail of Bits found 25 issues between the brew CLI and the backend CI/CD system; the latter includes use of pull_request_target and complex workflows which could be used by an insider to escalate privileges. Given the central nature of brew in many developer’s workflows, improving the security of Homebrew is a useful investment.
Progress and Efforts — Securing Package Registries
The OpenSSF publish a guest blog post with an update on some the work it’s doing engaging with the various language-specific package registries to harden security defenses while not, you know, breaking everything. The post includes a link to a handy spreadsheet tracking the completed and ongoing efforts across NPM, PyPI, Maven Central, NuGet, Composer, Conan, RubyGems, Crates, and Homebrew.
👀 Community and Public Sector Updates
Learn to Love the NVD Backlog
Two separate posts from VulnCheck and Fortress both analyze the CVE analysis backlog at NVD. While analysis has re-started with cooperation between NIST, CISA, and the public-private consortium work is underway, the rate of analysis is still below the rate of newly-published vulnerabilities, and it’s unlikely the backlog will be cleared before Christmas. Given that the current stats for accepted CVEs have about 20% of CVEs receiving some form of modification or rejection, the backlog of 16k CVEs probably means there are some exciting ones hiding out there.
See You At BlackHat?
I’ve heard that some security folks will be at Vegas next week (desert in August? of course!) for BlackHat. I’ll be there at the Stacklok booth if you want to chat, or if you’re just looking for me to a sign a copy of my book. I’ll also be happy to demo you Minder or Trusty, or talk about other security content, of course.
That’s all for this week! See you next Thursday…